PassLeader released the NEWEST CompTIA PT0-001 exam dumps recently! Both PT0-001 VCE dumps and PT0-001 PDF dumps are available on PassLeader, either PT0-001 VCE dumps or PT0-001 PDF dumps have the NEWEST PT0-001 exam questions in it, they will help you passing CompTIA PT0-001 exam easily! You can download the valid PT0-001 dumps VCE and PDF from PassLeader here: https://www.passleader.com/pt0-001.html (95 Q&As Dumps –> 158 Q&As Dumps –> 213 Q&As Dumps –> 258 Q&As Dumps)
Also, previewing the NEWEST PassLeader PT0-001 dumps online for free on Google Drive: https://drive.google.com/open?id=1Xvl7jQbsLhLfR0jZSB8jZLBFffBsoW1g
NEW QUESTION 76
A penetration tester is performing ARP spoofing against a switch. Which of the following should the penetration tester spoof to get the MOST information?
A. MAC address of the client.
B. MAC address of the domain controller.
C. MAC address of the web server.
D. MAC address of the gateway.
Answer: D
NEW QUESTION 77
A penetration tester observes that several high numbered ports are listening on a public web server. However, the system owner says the application only uses port 443. Which of the following would be BEST to recommend?
A. Transition the application to another port.
B. Filter port 443 to specific IP addresses.
C. Implement a web application firewall.
D. Disable unneeded services.
Answer: A
NEW QUESTION 78
A financial institution is asking a penetration tester to determine if collusion capabilities to produce wire fraud are present. Which of the following threat actors should the penetration tester portray during the assessment?
A. Insider threat
B. Nation state
C. Script kiddie
D. Cybercrime organization
Answer: D
NEW QUESTION 79
A penetration tester was able to enter an SQL injection command into a text box and gain access to the information store on the database. Which of the following is the BEST recommendation that would mitigate the vulnerability?
A. Randomize the credentials used to log in.
B. Install host-based intrusion detection.
C. Implement input normalization.
D. Perform system hardening.
Answer: D
NEW QUESTION 80
Which of the following properties of the penetration testing engagement agreement will have the largest impact on observing and testing production systems at their highest loads?
A. Creating a scope of the critical production systems.
B. Setting a schedule of testing access times.
C. Establishing a white-box testing engagement.
D. Having management sign-off on intrusive testing.
Answer: B
NEW QUESTION 81
A company requested a penetration tester review the security of an in-house-developed Android application. The penetration tester received an APK file to support the assessment. The penetration tester wants to run SAST on the APK file. Which of the following preparatory steps must the penetration tester do FIRST? (Choose two.)
A. Convert to JAR
B. Decompile
C. Cross-compile the application
D. Convert JAR files to DEX
E. Re-sign the APK
F. Attach to ADB
Answer: BC
NEW QUESTION 82
Consider the following PowerShell command:
……
Which of the following BEST describes the actions performed this command?
A. Set the execution policy
B. Execute a remote script
C. Run an encoded command
D. Instantiate an object
Answer: A
NEW QUESTION 83
Which of the following situations would cause a penetration tester to communicate with a system owner/client during the course of a test? (Choose two.)
A. The tester discovers personally identifiable data on the system.
B. The system shows evidence of prior unauthorized compromise.
C. The system shows a lack of hardening throughout.
D. The system becomes unavailable following an attempted exploit.
E. The tester discovers a finding on an out-of-scope system.
Answer: CE
NEW QUESTION 84
A penetration tester identifies the following findings during an external vulnerability scan:
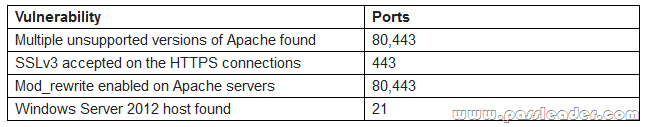
Which of the following attack strategies should be prioritized from the scan results above?
A. Obsolete software may contain exploitable components.
B. Weak password management practices may be employed.
C. Cryptographically weak protocols may be intercepted.
D. Web server configurations may reveal sensitive information.
Answer: A
NEW QUESTION 85
……
Welcome to choose PassLeader PT0-001 dumps for 100% passing CompTIA PT0-001 exam: https://www.passleader.com/pt0-001.html (95 Q&As VCE Dumps and PDF Dumps –> 158 Q&As VCE Dumps and PDF Dumps –> 213 Q&As VCE Dumps and PDF Dumps –> 258 Q&As VCE Dumps and PDF Dumps)
Also, previewing the NEWEST PassLeader PT0-001 dumps online for free on Google Drive: https://drive.google.com/open?id=1Xvl7jQbsLhLfR0jZSB8jZLBFffBsoW1g