PassLeader released the NEWEST CompTIA SY0-501 exam dumps recently! Both SY0-501 VCE dumps and SY0-501 PDF dumps are available on PassLeader, either SY0-501 VCE dumps or SY0-501 PDF dumps have the NEWEST SY0-501 exam questions in it, they will help you passing CompTIA SY0-501 exam easily! You can download the valid SY0-501 dumps VCE and PDF from PassLeader here: https://www.passleader.com/sy0-501.html (1218 Q&As Dumps –> 1235 Q&As Dumps –> 1292 Q&As Dumps –> 1318 Q&As Dumps –> 1366 Q&As Dumps –> 1423 Q&As Dumps –> 1472 Q&As Dumps) (Wrong Answers Have Been Corrected!!!)
Also, previewing the NEWEST PassLeader SY0-501 dumps online for free on Google Drive: https://drive.google.com/open?id=1Ei1CtZKTLawI_2jpkecHaVbM_kXPMZAu
QUESTION 16
Which of the following threat actors is MOST likely to steal a company’s proprietary information to gain a market edge and reduce time to market?
A. Competitor
B. Hacktivist
C. Insider
D. Organized crime
Answer: A
QUESTION 17
When trying to log onto a company’s new ticketing system, some employees receive the following message:
Access denied: too many concurrent sessions.
The ticketing system was recently installed on a small VM with only the recommended hardware specifications. Which of the following is the MOST likely cause for this error message?
A. Network resources have been exceeded.
B. The software is out of licenses.
C. The VM does not have enough processing power.
D. The firewall is misconfigured.
Answer: C
QUESTION 18
A network administrator at a small office wants to simplify the configuration of mobile clients connecting to an encrypted wireless network. Which of the following should be implemented if the administrator does not want to provide the wireless password or certificate to the employees?
A. WPS
B. 802.1x
C. WPA2-PSK
D. TKIP
Answer: A
QUESTION 19
A company is developing a new secure technology and requires computers being used for development to be isolated. Which of the following should be implemented to provide the MOST secure environment?
A. A perimeter firewall and IDS
B. An air gapped compiler network
C. A honeypot residing in a DMZ
D. An ad hoc network with NAT
E. A bastion host
Answer: B
QUESTION 20
Which of the following explains why vendors publish MD5 values when they provide software patches for their customers to download over the Internet?
A. The recipient can verify integrity of the software patch.
B. The recipient can verify the authenticity of the site used to download the patch.
C. The recipient can request future updates to the software using the published MD5 value.
D. The recipient can successfully activate the new software patch.
Answer: A
QUESTION 21
Drag and Drop
A security administrator is given the security and availability profiles for servers that are being deployed.
1) Match each RAID type with the correct configuration and MINIMUM number of drives.
2) Review the server profiles and match them with the appropriate RAID type based on integrity, availability, I/O, storage requirements.
Instructions:
– All drive definitions can be dragged as many times as necessary.
– Not all placeholders may be filled in the RAID configuration boxes.
– If parity is required, please select the appropriate number of parity checkboxes.
– Server profiles may be dragged only once.
If at any time you would like to bring back the initial state of the simulation, please select the Reset button. When you have completed the simulation, please select the Done button to submit. Once the simulation is submitted, please select the Next button to continue.

Answer:

Explanation:
1: RAID-0 is known as striping. It is not a fault tolerant solution but does improve disk performance for read/write operations. Striping requires a minimum of two disks and does not use parity. RAID-0 can be used where performance is required over fault tolerance, such as a media streaming server.
2: RAID-1 is known as mirroring because the same data is written to two disks so that the two disks have identical data. This is a fault tolerant solution that halves the storage space. A minimum of two disks are used in mirroring and does not use parity. RAID-1 can be used where fault tolerance is required over performance, such as on an authentication server. RAID-5 is a fault tolerant solution that uses parity and striping. A minimum of three disks are required for RAID-5 with one disk’s worth of space being used for parity information. However, the parity information is distributed across all the disks. RAID-5 can recover from a sing disk failure.
3: RAID-6 is a fault tolerant solution that uses dual parity and striping. A minimum of four disks are required for RAID-6. Dual parity allows RAID-6 to recover from the simultaneous failure of up to two disks. Critical data should be stored on a RAID-6 system.
http://www.adaptec.com/en-us/solutions/raid_levels.html
QUESTION 22
Refer to the following code:

Which of the following vulnerabilities would occur if this is executed?
A. Page exception
B. Pointer dereference
C. NullPointerException
D. Missing null check
Answer: D
QUESTION 23
A database backup schedule consists of weekly full backups performed on Saturday at 12:00 A.M. and daily differential backups also performed at 12:00 A.M. If the database is restored on Tuesday afternoon, which of the following is the number of individual backups that would need to be applied to complete the database recovery?
A. 1
B. 2
C. 3
D. 4
Answer: B
QUESTION 24
Which of the following technologies employ the use of SAML? (Select TWO.)
A. Single sign-on
B. Federation
C. LDAP
D. Secure token
E. RADIUS
Answer: AB
QUESTION 25
An organization is using a tool to perform a source code review. Which of the following describes the case in which the tool incorrectly identifies the vulnerability?
A. False negative
B. True negative
C. False positive
D. True positive
Answer: C
QUESTION 26
In a corporation where compute utilization spikes several times a year, the Chief Information Officer (CIO) has requested a cost-effective architecture to handle the variable capacity demand. Which of the following characteristics BEST describes what the CIO has requested?
A. Elasticity
B. Scalability
C. High availability
D. Redundancy
Answer: A
QUESTION 27
A security analyst is diagnosing an incident in which a system was compromised from an external IP address. The socket identified on the firewall was traced to 207.46.130.66:66. Which of the following should the security analyst do to determine if the compromised system still has an active connection?
A. tracert
B. netstat
C. ping
D. nslookup
Answer: B
QUESTION 28
Which of the following BEST describes an important security advantage yielded by implementing vendor diversity?
A. Sustainability
B. Homogeneity
C. Resiliency
D. Configurability
Answer: C
QUESTION 29
Drag and Drop
You have been tasked with designing a security plan for your company. Drag and drop the appropriate security controls on the floor plan.
Instructions: All objects must be used and all place holders must be filled Order does not matter. When you have completed the simulation, please select the Done button to submit.

Answer:
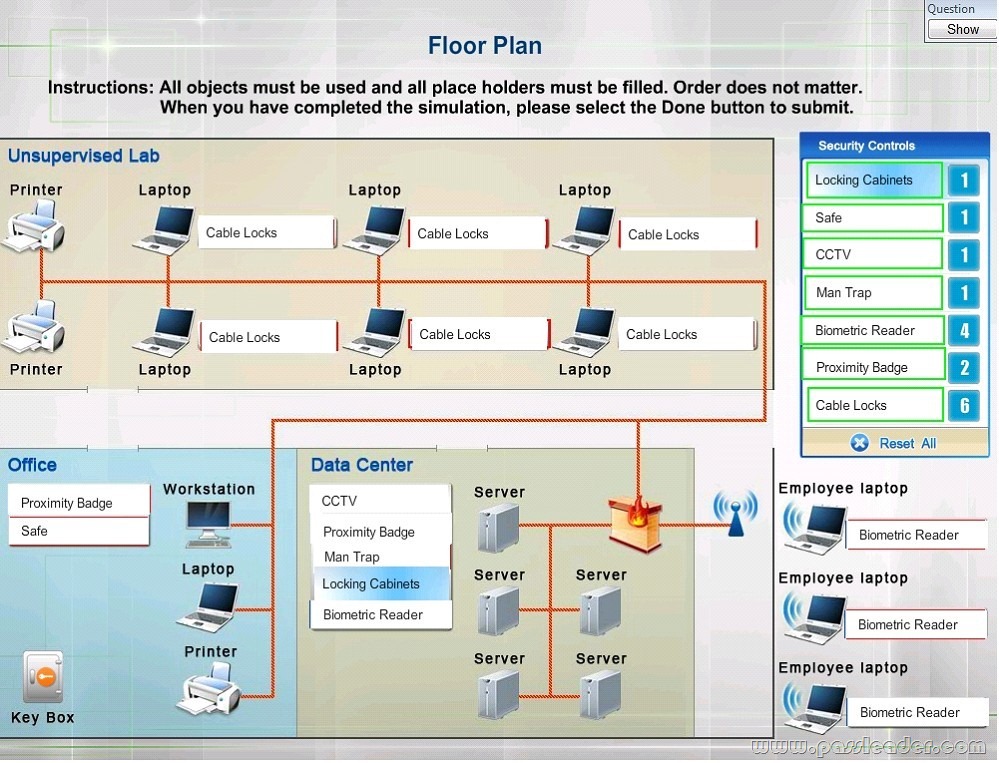
Explanation:
– Cable Locks can add a cable lock between a laptop and a desk prevents someone from picking it up and walking away.
– Safe is a hardware/physical security measure.
– Mantrap can be used to control access to sensitive areas.
– CCTV can be used as video surveillance.
– Biometric Reader can be used to control and prevent unauthorized access.
– Locking Cabinets can be used to protect backup media, documentation and other physical artefacts.
QUESTION 30
Which of the following encryption methods does PKI typically use to securely protect keys?
A. Elliptic curve
B. Digital signatures
C. Asymmetric
D. Obfuscation
Answer: B
Welcome to choose PassLeader SY0-501 dumps for 100% passing CompTIA SY0-501 exam: https://www.passleader.com/sy0-501.html (1218 Q&As VCE Dumps and PDF Dumps –> 1235 Q&As VCE Dumps and PDF Dumps –> 1292 Q&As VCE Dumps and PDF Dumps –> 1318 Q&As VCE Dumps and PDF Dumps –> 1366 Q&As VCE Dumps and PDF Dumps –> 1423 Q&As VCE Dumps and PDF Dumps –> 1472 Q&As VCE Dumps and PDF Dumps) (Wrong Answers Have Been Corrected!!!)
Also, previewing the NEWEST PassLeader SY0-501 dumps online for free on Google Drive: https://drive.google.com/open?id=1Ei1CtZKTLawI_2jpkecHaVbM_kXPMZAu