PassLeader released the NEWEST CompTIA CS0-001 exam dumps recently! Both CS0-001 VCE dumps and CS0-001 PDF dumps are available on PassLeader, either CS0-001 VCE dumps or CS0-001 PDF dumps have the NEWEST CS0-001 exam questions in it, they will help you passing CompTIA CS0-001 exam easily! You can download the valid CS0-001 dumps VCE and PDF from PassLeader here: https://www.passleader.com/cs0-001.html (252 Q&As Dumps –> 321 Q&As Dumps –> 373 Q&As Dumps –> 421 Q&As Dumps)
Also, previewing the NEWEST PassLeader CS0-001 dumps online for free on Google Drive: https://drive.google.com/open?id=0B-ob6L_QjGLpaXd6TXJ4T3ItSDQ (More SIMULATION questions, Drag and Drop questions, Hotspot questions)
QUESTION 55
A threat intelligence analyst who works for a technology firm received this report from a vendor:
“There has been an intellectual property theft campaign executed against organizations in the technology industry. Indicators for this activity are unique to each intrusion. The information that appears to be targeted is R&D data. The data exfiltration appears to occur over months via uniform TTPs. Please execute a defensive operation regarding this attack vector.”
Which of the following combinations suggests how the threat should MOST likely be classified and the type of analysis that would be MOST helpful in protecting against this activity?
A. Polymorphic malware and secure code analysis
B. Insider threat and indicator analysis
C. APT and behavioral analysis
D. Ransomware and encryption
Answer: B
QUESTION 56
The help desk informed a security analyst of a trend that is beginning to develop regarding a suspicious email that has been reported by multiple users. The analyst has determined the email includes an attachment named invoice.zip that contains the following files:
– Locky.js
– xerty.ini
– xerty.lib
Further analysis indicates that when the .zip file is opened, it is installing a new version of ransomware on the devices. Which of the following should be done FIRST to prevent data on the company NAS from being encrypted by infected devices?
A. Disable access to the company VPN.
B. Email employees instructing them not to open the invoice attachment.
C. Set permissions on file shares to read-only.
D. Add the URL included in the .js file to the company’s web proxy filter.
Answer: B
QUESTION 57
After running a packet analyzer on the network, a security analyst has noticed the following output:
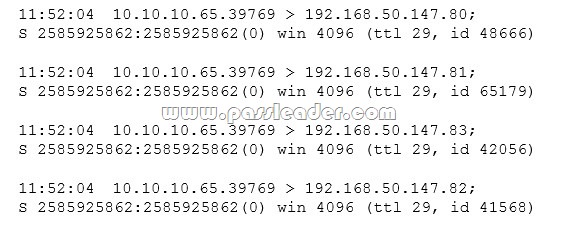
Which of the following is occurring?
A. A ping sweep
B. A port scan
C. A network map
D. A service discovery
Answer: B
QUESTION 58
A database administrator contacts a security administrator to request firewall changes for a connection to a new internal application. The security administrator notices that the new application uses a port typically monopolized by a virus. The security administrator denies the request and suggests a new port or service be used to complete the application’s task. Which of the following is the security administrator practicing in this example?
A. Explicit deny
B. Port security
C. Access control lists
D. Implicit deny
Answer: C
QUESTION 59
An organization has recently recovered from an incident where a managed switch had been accessed and reconfigured without authorization by an insider. The incident response team is working on developing a lessons learned report with recommendations. Which of the following recommendations will BEST prevent the same attack from occurring in the future?
A. Remove and replace the managed switch with an unmanaged one.
B. Implement a separate logical network segment for management interfaces.
C. Install and configure NAC services to allow only authorized devices to connect to the network.
D. Analyze normal behavior on the network and configure the IDS to alert on deviations from normal.
Answer: B
QUESTION 60
A cybersecurity analyst is reviewing the current BYOD security posture. The users must be able to synchronize their calendars, email, and contacts to a smartphone or other personal device. The recommendation must provide the most flexibility to users. Which of the following recommendations would meet both the mobile data protection efforts and the business requirements described in this scenario?
A. Develop a minimum security baseline while restricting the type of data that can be accessed.
B. Implement a single computer configured with USB access and monitored by sensors.
C. Deploy a kiosk for synchronizing while using an access list of approved users.
D. Implement a wireless network configured for mobile device access and monitored by sensors.
Answer: D
Welcome to choose PassLeader CS0-001 dumps for 100% passing CompTIA CS0-001 exam: https://www.passleader.com/cs0-001.html (252 Q&As VCE Dumps and PDF Dumps –> 321 Q&As VCE Dumps and PDF Dumps –> 373 Q&As VCE Dumps and PDF Dumps –> 421 Q&As VCE Dumps and PDF Dumps)
Also, previewing the NEWEST PassLeader CS0-001 dumps online for free on Google Drive: https://drive.google.com/open?id=0B-ob6L_QjGLpaXd6TXJ4T3ItSDQ (More SIMULATION questions, Drag and Drop questions, Hotspot questions)